搜索结果: 1-15 共查到“Ring”相关记录491条 . 查询时间(0.059 秒)
Drought impacts on tree carbon sequestration and water use - evidence from intra-annual tree-ring characteristics
carbon sequestration extreme drought intrinsic water-use efficiency physiological drought point dendrometer quantitative wood anatomys table carbon isotopes xylogenesis
2023/11/20
The impact of climate extremes on forest ecosystems is poorly understood but important for predicting carbon and water cycle feedbacks to climate. Some knowledge gaps still remain regarding how drough...

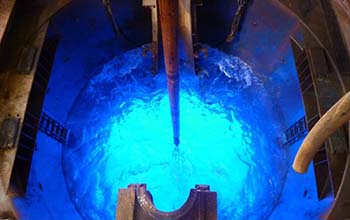
New black hole images reveal a glowing, fluffy ring and a high-speed jet(图)
黑洞图像 高速喷气机 等离子体物理学
2023/6/9
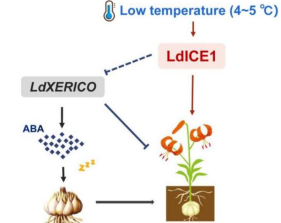
沈阳农业大学园艺学院观赏植物栽培生理团队揭示RING-H2型E3连接酶基因LdXERICO调控百合鳞茎休眠机制(图)
RING-H2型 E3连接酶 基因 LdXERICO 百合 鳞茎休眠
2023/4/14
近日,沈阳农业大学园艺学院观赏植物栽培生理团队在农林科学一区Top期刊Horticulture Research杂志上在线发表题为“The RING-H2 gene LdXERICO plays a negative role in dormancy release regulated by low temperature in Lilium davidii var. unicolor”的研究论文...
Sinking of Zealandia, Earth's hidden continent, linked to forging of the Pacific 'Ring of Fire'(图)
Sinking of Zealandia Earth hidden continent linked Pacific
2020/2/20
New findings from the expedition, funded largely by the U.S. National Science Foundation with contributions from more than 20 partner nations, were recently published in the Geological Society of Amer...
Soybean Oil Modified Bio-based Poly(vinyl alcohol)s via Ring-Opening Polymerization
Biodegradable properties Epoxidized soybean oil Modification Poly(vinyl alcohol)
2024/3/4
In this paper, a simple method to modify the poly(vinyl alcohol) (PVA) through ring-opening reaction of epoxidized soybean oil (ESBO), catalyzed by hydrochloric acid is reported. The effect of ESBO lo...
A hash function family is called correlation intractable if for all sparse relations, it hard to find, given a random function from the family, an input output pair that satisfies the relation. Correl...
Traceable and linkable ring signatures, traceable range proofs and applications on regulatable privacy-preserving blockchains
regulatable blockchain privacy preserving decentralization
2019/8/19
Privacy protection has been extensively studied in the current blockchain research field. As representations, Monero and Zerocash have realized completely anonymous and amount-hiding transactions. How...
Module-LWE versus Ring-LWE, Revisited
Lattice-based Cryptography Security Reduction Cyclotomic Fields
2019/8/19
Till now, the only reduction from the module learning with errors problem (MLWE) to the ring learning with errors problem (RLWE) is given by Albrecht et al.et al. in ASIACRYPT 20172017. Reductions fro...
Many cryptographic schemes have been proposed from learning with errors problems over some rings (Ring-LWE). Polynomial time quantum reduction from the approximating Shortest Independent Vectors Probl...
Onion Ring ORAM: Efficient Constant Bandwidth Oblivious RAM from (Leveled) TFHE
Homomorphic Encryption Oblivious RAM
2019/6/24
Oblivious RAM (ORAM) is a cryptographic primitive that allows a client to hide access pattern to its data encrypted and stored at a remote server. Traditionally, ORAM algorithms assume the server acts...
We describe an efficient linkable ring signature scheme, compact linkable spontaneous anonymous group (CLSAG) signatures, for use in confidential transactions. Compared to the existing signature schem...
Cryptanalysis of Ring Homomorphic Encryption Schemes
homomorphic encryption schemes quantum computing key-recovery attack
2019/6/3
We analyze the structure of finite commutative rings with respect to its idempotent and nilpotent elements. Based on this analysis we provide a quantum-classical IND-CCA^1 attack for ring homomorphic ...
Discretisation and Product Distributions in Ring-LWE
Ring-LWE Discretisation Homomorphic Encryption
2019/6/3
A statistical framework applicable to Ring-LWE was outlined by Murphy and Player (IACR eprint 2019/452). Its applicability was demonstrated with an analysis of the decryption failure probability for d...
Omniring: Scaling Up Private Payments Without Trusted Setup - Formal Foundations and Constructions of Ring Confidential Transactions with Log-size Proofs
Ring Confidential Transactions Log-size Proofs
2019/5/31
Monero is the largest cryptocurrency with built-in cryptographic privacy features. The transactions are authenticated using spend proofs, which provide a certain level of anonymity by hiding the sourc...
(Linkable) Ring Signature from Hash-Then-One-Way Signature
ring signature linkable ring signature lattice-based cryptography
2019/5/28
In this paper, we revisit the generic construction of ring signatures from hash-then-one-way type (Type−HType−H) signatures proposed by Abe et al. (AOS) in 2004 and made the following cont...


